An increasingly popular technology for extending cell-phone coverage ranges had a major security hole that went undetected for years, through which an attacker could eavesdrop on everything a target did on their phone, according to new research released on Monday.
The research brings to light previously unknown vulnerabilities in some models of femtocells, devices that mobile network operators use to bring wireless service to low-coverage zones. The compact boxes, which are typically as small as a standard cable modem, can be deployed in hard-to-reach spots like the top of an apartment building or a home in the mountains. Femtocells are also referred to as "network extenders," and analysts project that as many as 50 million of them will be in use by 2014.
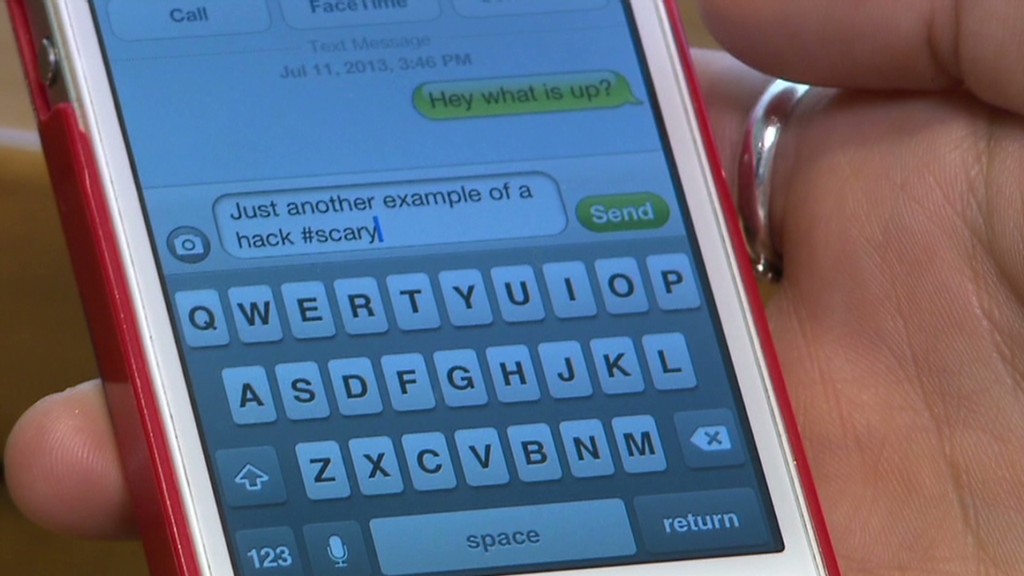
In a demonstration for CNNMoney, researchers at iSEC Partners, who discovered the security hole, covertly recorded one of our phone conversations and played it back for us. They were also able to record our browsing history, text messages, and even view pictures we sent from one smartphone to another by hacking the network extender.
"We see everything that your phone would send to a cell phone tower: phone calls, text messages, picture messages, mobile Web surfing," said iSEC Partners senior security consultant Tom Ritter.
ISEC discovered the security flaw a year ago and contacted the affected vendors, who quickly began working on a fix. Though iSEC focused its research on femtocells operating on Verizon's 3G CDMA network, the company believes similar holes could exist on other network extenders.
A Verizon (VZ) spokesman said the problem has been repaired in all of the femtocells it is currently using. ISEC used a modified femtocell that did not receive a patch to the security flaw.
"The demonstration CNN saw was for an identified issue that was fixed earlier this year on all network extender devices," the company said in a written statement. "The fix prevents the network extender from being compromised in the same manner."
Verizon said it has not received any customer complaints about the security glitch.
Samsung, the company that manufactures Verizon's network extenders, also issued a statement saying the problem has been fixed. ISEC plans to show off more details of its hack later this month at the Black Hat and Def Con security conferences in Las Vegas.
Security researchers say these kinds of flaws are inevitable. As new technologies get more powerful, though, the risks get bigger.
"Once you first saw this product was available, you said, 'If there are any vulnerabilities, it'll be really bad," hacker Chris Wysopal, the chief technology officer for security software maker Veracode.
When he learned about femotcells, he says he immediately thought: "Somebody's bound to break this."
ISEC, which specializes in security research, says the attack it pioneered doesn't require very sophisticated hacking.
"You do need some level of technical skills, but people are learning those skills in college," Ritter said. "Breaking into one of these devices, or a device like this, is within the realm of people working at home."
Since it would be impractical for a passer by to randomly hack your femtocell, this exploit is more in the realm of hypothetical than likely -- even before the security patch went out. But femtocells and other "small cell" technologies are increasingly being deployed in businesses, homes, malls, stadiums and other public areas. If security flaws exist, it's important that the manufacturers are made aware of them.
Security pros say that using encryption apps like Wickr, Cellcrypt, Redphone and TextSecure can help users looking for a more secure connection. But researchers at iSEC have resigned themselves to the idea that nothing is confidential.
"You should assume that everything you're saying is being intercepted," said Doug DePerry, one of the company's senior consultants. "That is a bit of a defeatist opinion, but sometimes that has to be the way it is."

